Discover our latest posts
Welcome to the flameera blog! Here you will find everything you need to know about cybersecurity. Our blog is dedicated to providing you with expert information, practical tips, and the latest industry news.

MDR: Expanding Visibility Beyond the Endpoint
At Flameera, we understand that protecting our clients’ digital assets requires a combination of visibility, intelligence, and responsiveness. That’s …
Agile Development and Cybersecurity
Speed is an essential value in software development. Delivering new features frequently, responding to market changes, and adapting to user needs in …

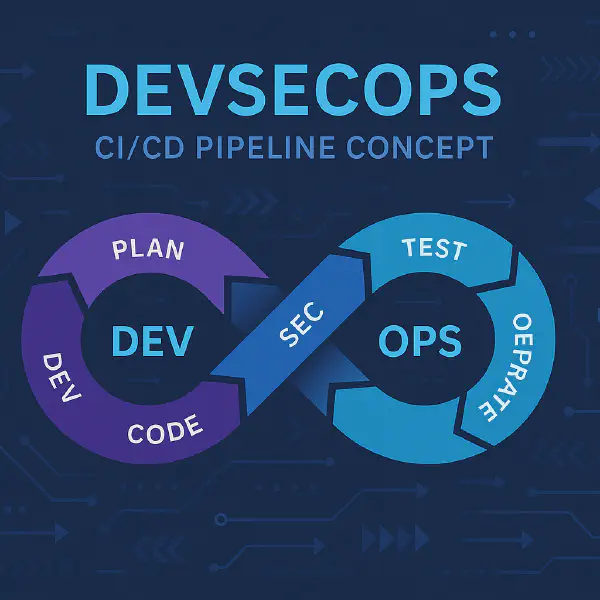
Security in the Software Development Lifecycle
Integrating security into the Secure Software Development Lifecycle (sSDLC) is key to protecting applications, reducing risks in the software supply …
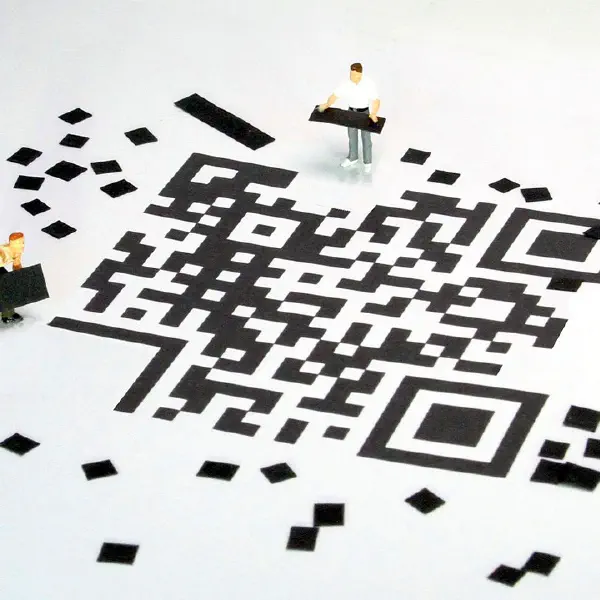
Did You Scan a QR Code Without Thinking?
QR codes are everywhere: restaurants, transportation, advertisements… and, unfortunately, also in cyberattacks. Their ease of use has made this …

How to act in case of ransomware
Ransomware is a type of malicious software designed to deny access to a user’s systems or data by encrypting files. Once ransomware has infected …

Data Breaches: The Hidden Threat
Currently, all companies, including small and medium-sized enterprises (SMEs), face a growing threat: data breaches. Daily news reports highlight new …

Third-Party Risk Management for SMEs
Small and medium-sized enterprises (SMEs) heavily rely on external suppliers to enhance their operations and offer specialized services, as they …

Ransomware: Understanding How It Works
A few days ago, we learned the news that the leader of the cybercriminal group LockBit 1, one of the largest malicious actors dedicated to ransomware, …

Common Cybersecurity Threats Faced by SMEs
As we already know, small and medium-sized enterprises (SMEs) are increasingly being targeted by cybercriminals. Despite their smaller size, SMEs …

Cybersecurity in SMEs: A Guide for Entrepreneurs
Small and medium-sized enterprises (SMEs) are becoming prime targets for cybercriminals. Gradually, entrepreneurs are understanding the importance of …